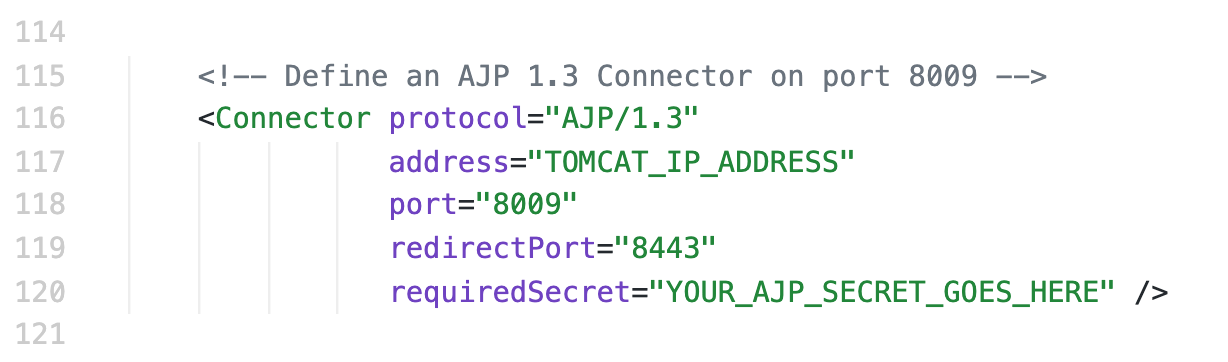
GitHub - markquinn12/springBoot-JHipster-AJP-Port: Example of how to open an AJP port in a spring boot (tomcat) angular webapp
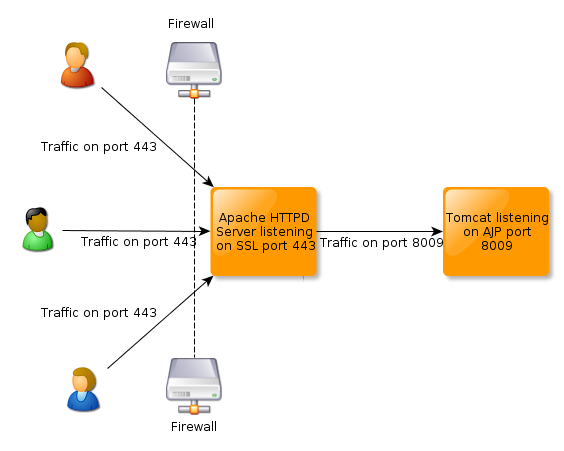
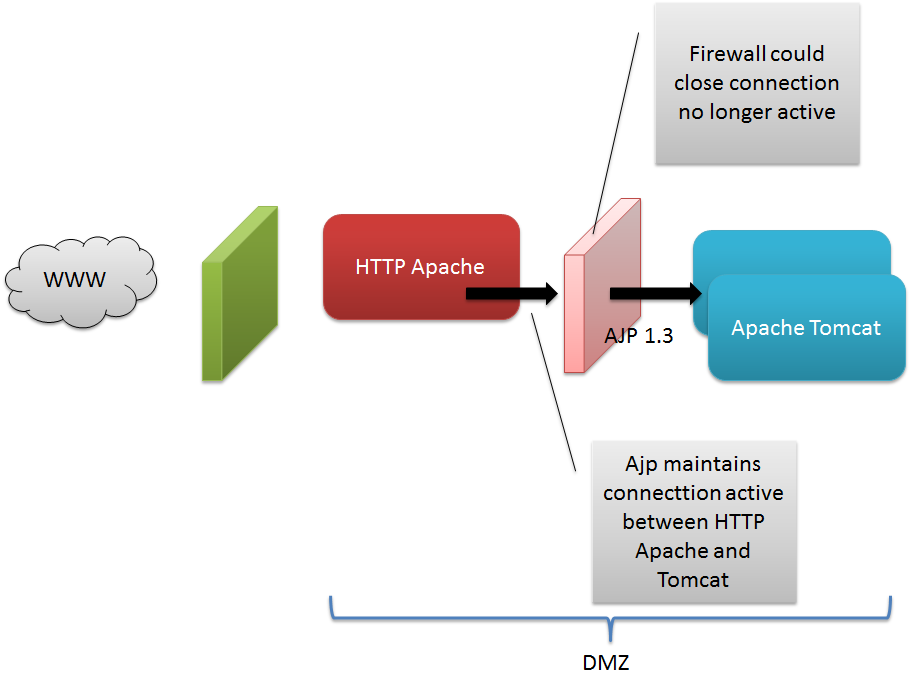
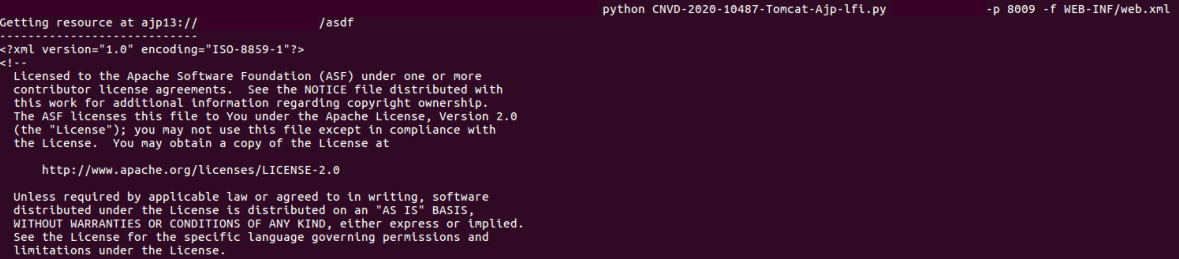
CVE-2020-1938: Ghostcat - Apache Tomcat AJP File Read/Inclusion Vulnerability (CNVD-2020-10487) - Blog | Tenable®
What Is CVE-2020-1938: Ghostcat - Apache Tomcat AJP File Read/Inclusion Vulnerability | Markvision Enterprise